Blog
Why Traditional Backups Fail Against Modern Adversaries
For years, organisations operated under the assumption that backups were a reliable safety net. The logic was simple: if something went wrong, the backups would save the day. However, that assumption no longer holds in a landscape defined by ransomware, insider threats, and cloud-complexity.
The hard truth is that many traditional backup strategies fail exactly when they are needed most. When an organisation is under attack.

Where Traditional Backup Defences Break Down
Traditional backup strategies were designed in an era of hardware failures and accidental deletions. They did not account for modern adversaries who understand that if they control your backups, they control your recovery. If an attacker gains privileged access, your backups often become just another target. This is why traditional backups fail against modern adversaries. At Covenco, we see several common points of failure:
- Writable Backups: Most systems allow for deletion, overwriting or changes to retention policies.
- Compromised Credentials: Attackers use stolen domain credentials or shared admin accounts to use your own tools to destroy recovery options.
- Logical Manipulation: An adversary can shorten retention windows or force cleanup jobs so the system deletes data automatically.
- Discovered Too Late: Many businesses only discover corrupted data or missing dependencies during the high-pressure environment of a live recovery attempt.
The New Standard: Immutable Backup Resilience
Immutable backup has moved from a ‘nice to have’ to a business-critical requirement. In simple terms, once backup data is written, it cannot be altered, deleted or encrypted, even by an administrator.
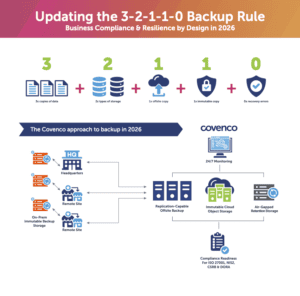
This is the ‘1’ in the 3-2-1-1-0 rule, typically enforced through Write-Once, Read-Many (WORM) storage or object lock mechanisms. It removes the attacker’s leverage, preserves a clean recovery point, and significantly reduces the pressure to pay a ransom. Read our 3-2-1-1-0 blog to see how this framework aligns your business with modern data resiliency standards.
Immutability protects the data, but it is not magic. To satisfy the ‘0’ in the 3-2-1-1-0 rule (zero recovery errors) immutability must be paired with constant monitoring and rigorous, regular testing.
For organisational leadership, this is no longer a ‘tick list’ item; it is a core pillar of resilience and supply chain compliance. You must be able to answer the question: ‘Would our backups survive an attacker with admin access?’.
At Covenco, we ensure your recovery is smarter, faster, and clean. Our fully planned and orchestrated DR solutions offer:
- Initial Replication: Data is made available from our secure UK data centre in a first instance response.
- Clean Hardware Recovery: To prevent ransomware from attacking from within during restoration, we provide recovery to clean hardware that can be shipped directly to your site.
- Cloud Recovery: Alternatively, we can recover your environment to a cloud instance if preferred.
Working with Covenco allows your company to stay ahead of evolving threats while ensuring you meet the strict compliance expectations of your customers and partners.
The Zero Recovery Error Checklist
To achieve a ‘Zero Recovery Error’ status, your organisation must move beyond the ‘set and forget’ mindset of traditional backups. This stage of the 3-2-1-1-0 rule is specifically focused on the ability to restore data without errors during a live incident.
Below is a technical checklist designed to align your recovery posture with the requirements of NIS2, DORA, and the UK CSRB.
Technical Checklist for ‘Zero Recovery Error’ Status
1. Integrity and Verification
- Automated Boot Verification: Implement automated testing that boots virtual machines (VMs) in an isolated environment to confirm the OS and heartbeat are functional.
- Checksum Validation: Perform regular integrity checks to ensure that the data written to the backup media matches the source and has not been corrupted or altered.
- Application-Level Testing: Verify that not only the data but also the specific application dependencies (e.g., database services, API links) are functional upon restoration.
2. Immutable and Air-Gapped Infrastructure
- WORM Storage Implementation: Ensure your primary recovery copy is stored on Write-Once, Read-Many (WORM) media or uses S3 Object Lock to prevent encryption by attackers.
- Logical or Physical Air-Gapping: Maintain at least one copy of data that is completely isolated from the production network to break the ransomware cycle.
- Identity and Access Management (IAM): Enforce multi-factor authentication (MFA) and separation of duties so that no single administrator has the authority to both create and delete backups.
3. Orchestration and Clean Recovery
- Pre-defined Recovery Workflows: Document and automate the sequence of restoration (e.g., domain controllers first, then databases, then applications) to eliminate manual errors under pressure.
- Clean-Room Environment: Establish a ‘clean’ recovery environment (either via Covenco’s hardware shipping service or a dedicated cloud instance) to ensure malware cannot re-infect systems during the restore process.
- Scalability Testing: Audit whether your recovery hardware or cloud environment can handle the full production load, not just a subset of data.
4. Audit and Compliance Documentation
- Frequent Testing Cycles: Move from annual DR tests to monthly or quarterly automated ‘fire drills’ to satisfy DORA and CSRB supply chain requirements.
- Recovery Time Objective (RTO) Validation: Provide documented proof that your actual recovery speed matches the business requirements and regulatory mandates.
- Tamper Logging: Maintain immutable logs of all backup access and modification attempts to provide to auditors as proof of resilience.
Get in touch with Covenco
If this has raised questions about how your organisation would perform under a real incident or a formal audit, there are two simple next steps. If you would like to go deeper into what auditors, regulators and insurers will expect in 2026, join our upcoming live roundtable:
Surviving the Audit: live roundtable + Q&A (45-60 minutes)
How to prove recoverability with immutable backup and verified recovery workflows. Find out more and register: https://covenco.com/data-management-services/surviving-the-audit/
If you would prefer a direct conversation, we can help you assess your current backup and recovery posture, identify gaps, and design an immutable, tested recovery model aligned to your risk profile and regulatory obligations.
Speak to the Covenco team about your backup and recovery challenges and explore your options. Get in touch with Covenco today to start building a more resilient, audit-ready recovery capability.